- What Is a Crypto Pockets Tackle?
- How Does a Crypto Pockets Tackle Work?
- Create a Pockets Tackle?
- Sorts of Crypto Pockets Addresses
- Discover Your Pockets Tackle?
- Ship and Obtain Crypto Utilizing a Pockets Tackle?
- Is It Protected to Share Your Pockets Tackle?
- Hold Your Pockets Tackle and Funds Safe?
- Widespread Pockets Tackle Errors to Keep away from
- Conclusion
- FAQs
What’s a pockets handle? It’s a distinctive identifier product of letters and numbers that helps you obtain and ship crypto on a blockchain. Its construction varies throughout cryptocurrencies as each community follows a singular pockets handle format.
On this information, we’ll delve deeper into crypto pockets addresses and their sorts. We’ll additionally present a step-by-step information on the way to get a pockets handle and security tricks to handle funds effectively.
What Is a Crypto Pockets Tackle?
A cryptocurrency pockets handle is a singular string of alphanumeric characters. Many addresses, particularly these on Ethereum and EVM chains, are hexadecimal, that means they encompass numbers 0-9 and letters A-F. Furthermore, sure blockchains are case-sensitive (e.g., Solana) or might require a vacation spot tag (e.g., Ripple).
How Does a Crypto Pockets Tackle Work?

A crypto pockets handle is analogous to an electronic mail handle. An e-mail ID helps you ship and obtain messages. Equally, a pockets handle allows you to ship and obtain crypto to and from different customers.
To confirm the safety and authenticity of cryptocurrency transactions, pockets addresses leverage cryptographic algorithms. Moreover, these addresses are pseudonymous. They conceal your identification, enhancing anonymity and privateness.
If you create a pockets, the platform/utility generates an unique handle for you. Every crypto handle includes two essential elements: a public key and a non-public key.
Public keys are corresponding to checking account numbers which can be particular to every consumer and could be shared with everybody. Personal keys are akin to ATM PINs. They’re secret codes that should be saved confidential to stop unauthorized utilization of funds. Furthermore, you require personal keys to entry the digital belongings saved in your pockets, signal blockchain transactions, and decrypt knowledge.
Cryptocurrency wallets routinely generate cryptographic key pairs (private and non-private keys) and retailer them securely. They use encryption algorithms to generate a public key out of your personal key. Additionally they computationally derive a hashed and shortened model of your public key, which turns into your pockets handle.
If you provoke a transaction, it’s verified by the community utilizing cryptography and consensus protocols. Nonetheless, belongings transferred to the fallacious pockets addresses can’t be recovered — at all times double-check earlier than sending.
Create a Pockets Tackle?
Step 1: Choose a crypto pockets
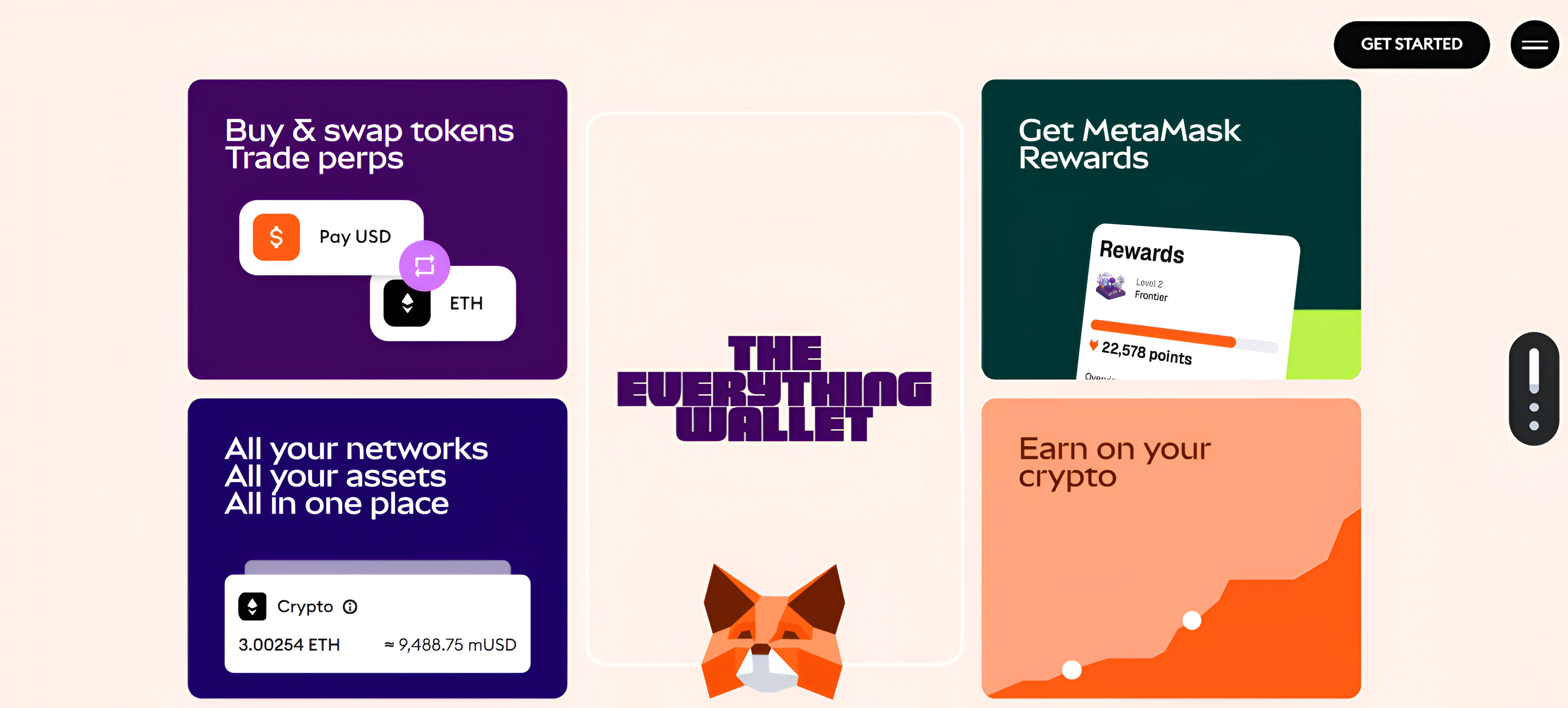
Based mostly in your preferences, choose an appropriate blockchain pockets. If you’d like a 3rd occasion to safeguard your funds, select custodial wallets like Kraken or Gemini. If you’d like full management of your personal keys, go for non-custodial wallets like Metamask or Phantom. For offline storage of cryptocurrencies, think about {hardware} wallets corresponding to Trezor or Ledger.


Step 2: Select a digital asset
Relying on the cryptocurrency you’re about to obtain, create a suitable pockets handle. For instance, you’ll want an Ethereum pockets handle to obtain ETH tokens.
Step 3: Generate a pockets handle
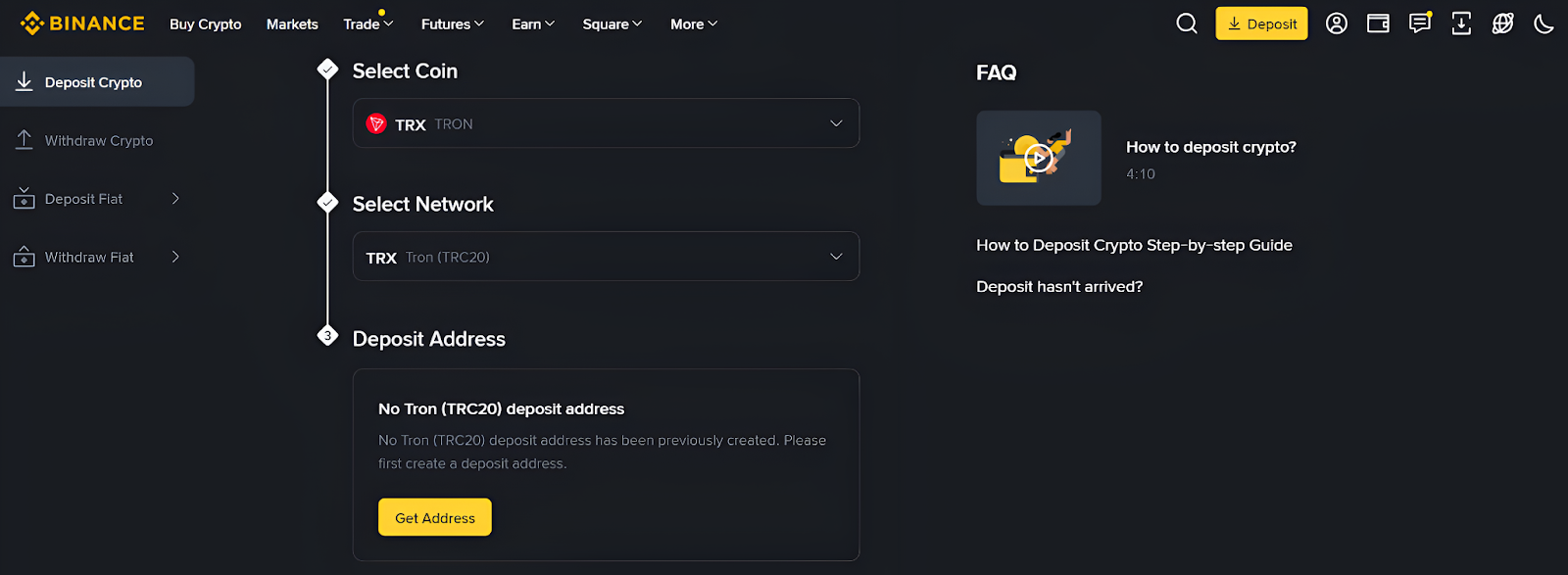
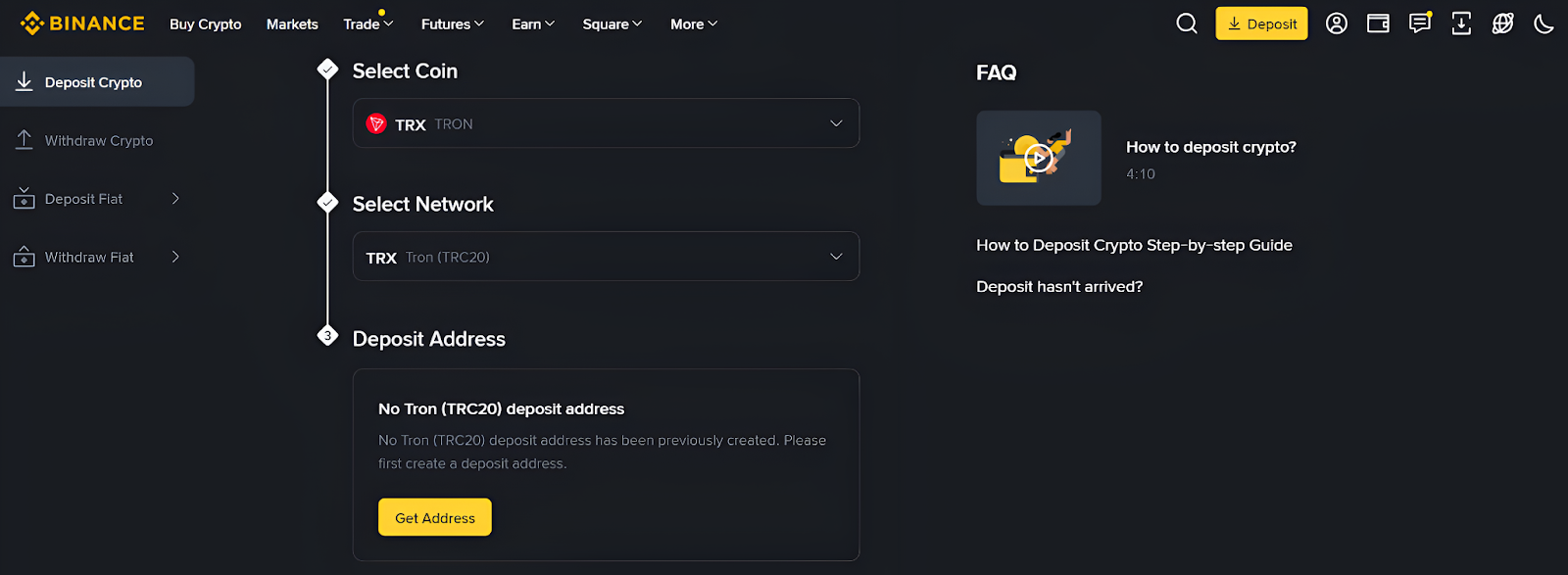
Think about you wish to create a Tron handle to obtain TRX tokens in your crypto pockets on Binance. To proceed, comply with the steps under:
- Go online to your Binance account and click on the “Deposit” tab.
- Choose TRX cash and the TRC20 community.
- Click on the “Get Tackle” tab. The pockets will immediately generate a TRC20 deposit handle.
- Copy and share this handle with the sender.
Sorts of Crypto Pockets Addresses
Bitcoin Pockets Addresses (BTC)
A Bitcoin pockets handle is a definite mixture of letters and numbers used to execute BTC transactions. You want a Bitcoin-compatible pockets to obtain BTC funds and work together with the Bitcoin blockchain. There are primarily three sorts of Bitcoin pockets addresses:
- Pay-to-Public-Key-Hash (P2PKH): That is the legacy script sample and the unique Bitcoin handle construction, which begins with 1. It permits customers to ship Bitcoin (BTC) to the hash of a pockets’s public key, quite than the general public key itself.
Instance: “1FfmbHfnpaZjKFvyi1okTjJJusN455paPH”
- Pay-to-Script-Hash (P2SH): This handle construction begins with 3 and permits you to lock BTC to a script hash, as an alternative of a public key. It’s suitable with each non-SegWit (P2PKH) and SegWit (Bech32) addresses.
As an illustration: “3J98t1WpEZ73CNmQviecrnyiWrnqRhWNLy”
- Bech32: These are the native SegWit addresses that begin with “bc1”. Although they’re case-sensitive, they’re shorter and facilitate extra environment friendly transaction processing. They assist scale back crypto transaction prices significantly and have a built-in checksum to detect errors.
Instance: “bc1qw508d6qejxtdg4y5r3zarvary0c5xw7kygt080”
Ethereum Pockets Addresses (ETH)
Ethereum addresses are 42-character alphanumeric strings prefixed with “0x”, serving to customers ship/obtain ERC-20 tokens and Ethereum-based digital belongings. They help good contracts, dApps, and DeFi protocols.
Instance: “0x4e3b2a1F9C6D8B7E5A0F2cD91E8B4a6f3C7D2A9E”
Different Widespread Pockets Addresses
- Litecoin: LTC receiving addresses start with an L or M and alter routinely for each transaction in most crypto wallets.
- Solana: Solana addresses are 32-44-character Base58-encoded strings that act as distinctive identifiers on the SOL community.
- Cardano: An ADA handle is created by hashing your public key utilizing the Blake2b-224 algorithm. Often, it makes use of the prefix “addr1”.
Discover Your Pockets Tackle?
- Open your crypto pockets desktop/cell utility.
- Click on the “Deposit” button and select “Deposit crypto” from the dropdown menu.
- Choose the token and community for which you wish to discover a pockets handle. The handle can be instantly displayed on the display.
- Copy the handle or scan the QR code rigorously.
- Double-check should you’ve shared the right handle with the sender.
Ship and Obtain Crypto Utilizing a Pockets Tackle?
To ship cryptocurrencies to somebody, you should first request their crypto pockets handle. When you get hold of the required particulars, enter the recipient’s handle accurately in your pockets utility or software program. Specify the coin and quantity you want to ship. Moreover, choose the right community.
The software program/app will auto-calculate and show the community/fuel charges you have to incur to execute a cryptocurrency transaction. Evaluate the transaction particulars and charges. If right, hit the “Affirm” tab. Your ship transaction will now be broadcast to the community for verification. As soon as validated, the transaction can be recorded in a block and added to the blockchain.
To obtain cryptocurrencies, you have to share your public pockets handle with the sender. The sender will enter your handle of their pockets app together with different particulars like token, quantity, and community. As soon as the sender’s transaction is authorised by the community, the funds can be credited to your pockets.
Is It Protected to Share Your Pockets Tackle?
Sure. It’s completely protected to share your handle with others. Furthermore, you should disclose your pockets handle to obtain cryptocurrency funds. So long as your personal keys and restoration phrases aren’t compromised, no person can entry your funds. Your identification or enterprise title additionally stays hidden.
Nonetheless, blockchain explorers like Etherscan, Solscan, and Polygonscan show the transaction histories linked to a specific public handle. As cryptocurrencies are designed to report transactions on immutable, clear ledgers, you possibly can’t cease explorers from monitoring your pockets actions.
To facilitate smoother crypto funds, organizations usually show pockets addresses on their web sites, QR codes, and invoices. For enhanced safety, some companies create distinctive addresses for every transaction.
Moreover, self-custody pockets addresses grant you full management over your personal keys. They don’t require identification verification and are much less liable to cyber assaults than custodial wallets.
Hold Your Pockets Tackle and Funds Safe?
- Select famend digital wallets: All the time choose well-known Web3 wallets with cutting-edge safety features like multi-party computation, safety fund, and so forth. Earlier than downloading a pockets app, examine consumer suggestions on respected assessment platforms corresponding to Trustpilot and Reddit.
- Retailer personal keys offline: Backup your personal keys in {hardware} wallets like Trezor and Ledger. As they aren’t related to the web, they aren’t uncovered to on-line threats.
- Double-check transaction particulars: If you’re sending funds, make sure the transaction quantity and the recipient’s pockets handle are entered precisely. Additionally, examine whether or not you’ve chosen the suitable token. Whereas receiving crypto, make sure you’ve shared the right pockets handle akin to the cryptocurrency you’re about to obtain.
- Replace pockets software program: By usually updating your pockets software program, you’ll achieve entry to the newest options and safety protocols. Wallets with out the newest updates are extra prone to hacks.
- Allow multi-factor authentication: Most crypto wallets require customers to endure a number of ranges of verification to entry their funds. These embrace a safe password, e-mail verification, and a Google Authenticator code.
- Prohibit transactions to whitelisted addresses: Many wallets, like Bitget and Coinbase, will let you whitelist trusted pockets addresses. This function serves as an extra safety layer on your funds.
Widespread Pockets Tackle Errors to Keep away from
- Transferring cryptocurrencies to the fallacious addresses: Should you ship crypto to incorrect addresses, your funds can be misplaced endlessly, with zero possibilities of restoration.
- Copy-paste, typo, or scanning errors: Since pockets addresses are lengthy and sophisticated, use area title providers to shorten them and keep away from typing them manually. Even when a single character is lacking within the handle, you could lose your cash. Both you’ll find yourself sending belongings to the fallacious recipient or fail to obtain funds. Furthermore, malicious QR codes usually include fraudulent addresses. Thus, whether or not you copy-paste or scan, double-check pockets addresses earlier than initiating transactions.
- Sharing your personal keys: Dropping your personal keys is akin to dropping your crypto belongings completely. Due to this fact, by no means share your personal keys with anybody and keep away from storing them in software program wallets.
- Utilizing the identical handle for a number of transactions: As pockets addresses are publicly seen, generate a brand new handle for every transaction. Keep away from reusing the identical pockets handle repeatedly to discourage scammers from fraudulently stealing your funds. If you’d like extra anonymity, use hierarchy deterministic wallets. They routinely generate distinct addresses from a single restoration phrase.
Conclusion
Pockets addresses function locations for receiving funds. They encompass a singular string of characters and are corresponding to checking account numbers. Plus, every blockchain’s pockets handle has its personal format. In essence, understanding pockets addresses is essential to choosing the proper blockchain pockets for safeguarding your cryptocurrencies.
FAQs
Every blockchain has a singular handle format. Sometimes, pockets addresses include numbers and higher/decrease case letters. An instance of a pockets handle could be “rP1Cosk2Z7v3T3h5N6yZJZyGqj1n5bX9K”.
No. Your pockets handle is a hashed and shortened model of your public key. The hash makes your handle shorter whereas guaranteeing it’s linked to the right key pair.
As cryptocurrency transactions are recorded on publicly verifiable blockchains, your pockets handle could be traced. It’s also doable to decode the true identification of customers primarily based on their pockets actions. Nonetheless, with out your personal keys or restoration phrase, nobody can entry your funds even when they know your pockets handle.
Whether or not your pockets handle stays unchanged is determined by the blockchain on which the crypto asset exists. For instance, Ethereum addresses are static, whereas Bitcoin generates a brand new handle for every transaction.
Should you lose entry to your pockets handle, you possibly can restore entry utilizing your restoration phrase or personal key. Nonetheless, should you’ve forgotten your personal key and didn’t keep a backup, your funds will stay inaccessible endlessly. Keep away from such conditions by enabling multi-user entry controls, exporting seed phrases, and assigning admin-level retrieval choices. Additionally, select crypto wallets with built-in backup instruments. For added safety, create a brand new pockets handle for each shopper/transaction and block suspicious addresses.
Your pockets handle is like your checking account quantity or e-mail ID. No one can hack your pockets utilizing your handle, until they pay money for your personal keys or seed phrase.