In 2025, attackers drained billions of {dollars} from Web3 wallets. Most often, the underlying blockchain infrastructure was not compromised. As an alternative, losses occurred as a result of customers unknowingly authorized malicious sensible contract interactions.
{Hardware} wallets defend personal keys, and antivirus software program helps forestall conventional malware. Nevertheless, neither is designed to interpret sensible contract logic. When a person indicators a transaction, a pockets confirms the signature request, not the intent behind it.
This highlights a structural distinction between conventional digital safety and Web3 safety. Blockchain transactions are clear however irreversible, and malicious contracts can seem reliable at first look. Because of this, Web3 requires safety instruments particularly designed to research on-chain conduct earlier than transactions are executed.
This information outlines key Web3 safety instruments related in 2026 and explains how they deal with dangers distinctive to blockchain environments.
Why Web3 Safety Is Totally different
Web3 safety differs basically from conventional on-line safety fashions. Understanding these variations is crucial for managing digital property safely.
{Hardware} wallets have restricted scope
{Hardware} wallets similar to Ledger or Trezor safe personal keys from exterior compromise. Nevertheless, they don’t consider transaction intent.
If a person approves a malicious transaction, the pockets processes the request as instructed. The system secures entry, however decision-making stays the person’s duty.
Blockchain transactions are irreversible
In contrast to conventional banking methods, blockchain transactions can’t be reversed. As soon as a transaction is signed and confirmed, property are transferred completely. This makes pre-transaction evaluation particularly necessary in Web3 environments.
Conventional antivirus software program is inadequate
Antivirus instruments are designed to detect identified malware patterns in information and executables. They don’t interpret sensible contract code or blockchain permissions.
Understanding capabilities similar to token approvals or asset transfers requires instruments which might be conscious of blockchain-specific dangers.
Important Web3 Safety Instruments
The next instruments give attention to stopping widespread Web3-related threats by analyzing contracts, permissions, and transaction conduct earlier than execution.
1. Kerberus
Kerberus is a browser-based safety device designed to research sensible contracts and decentralized purposes in actual time. It makes use of an AI system known as Sentinel3 to scan web sites and contracts earlier than pockets connections are authorized.
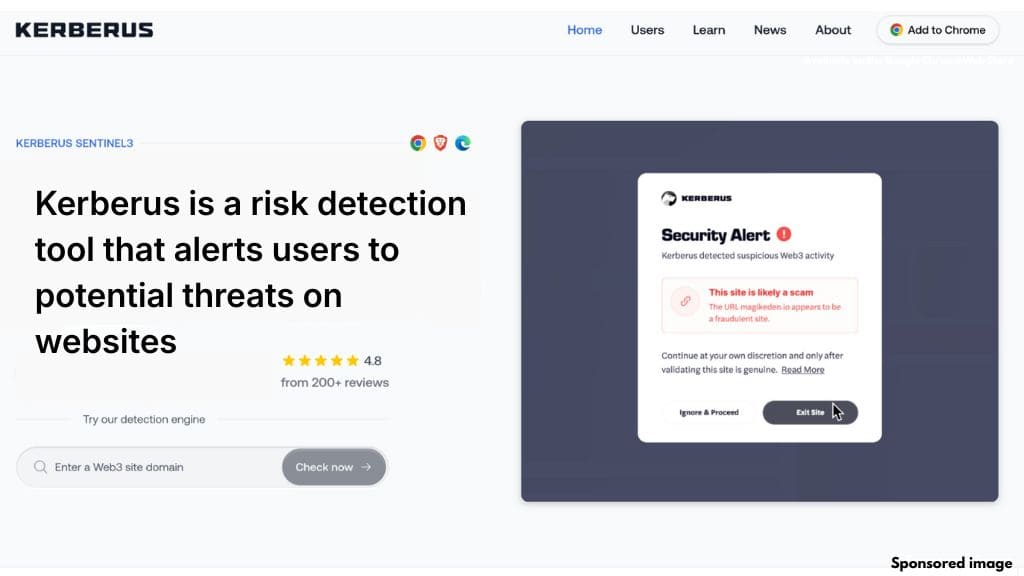
Somewhat than relying solely on static blocklists, Sentinel3 evaluates behavioral patterns to establish beforehand unseen threats. This method permits it to flag potential dangers even when contracts haven’t but been extensively reported.
Kerberus helps over 1,000 EVM-compatible networks and has expanded protection to Solana. The extension operates within the background and solely alerts customers when potential points are detected.
The platform additionally presents transaction protection via the Fairside community, offering an extra layer of safety in sure eventualities. Superior options can be found via its premium providing.
2. Pocket Universe
Pocket Universe focuses on transaction transparency. Earlier than a transaction is signed, the device simulates its execution on a forked model of the blockchain. This permits customers to preview outcomes with out risking funds.
The outcomes are displayed in clear language, outlining asset actions and permission adjustments. This helps customers perceive precisely what a transaction will do, together with whether or not it grants ongoing entry to tokens or NFTs.
Pocket Universe is efficient at figuring out widespread exploit patterns similar to permission abuse, signature-based NFT drains, and restrictive token contracts. Its transaction preview performance is designed to scale back approval-related errors.
3. Revoke.money
Revoke.money addresses dangers related to token approvals. Many decentralized purposes require customers to grant spending permissions, which regularly stay lively indefinitely.
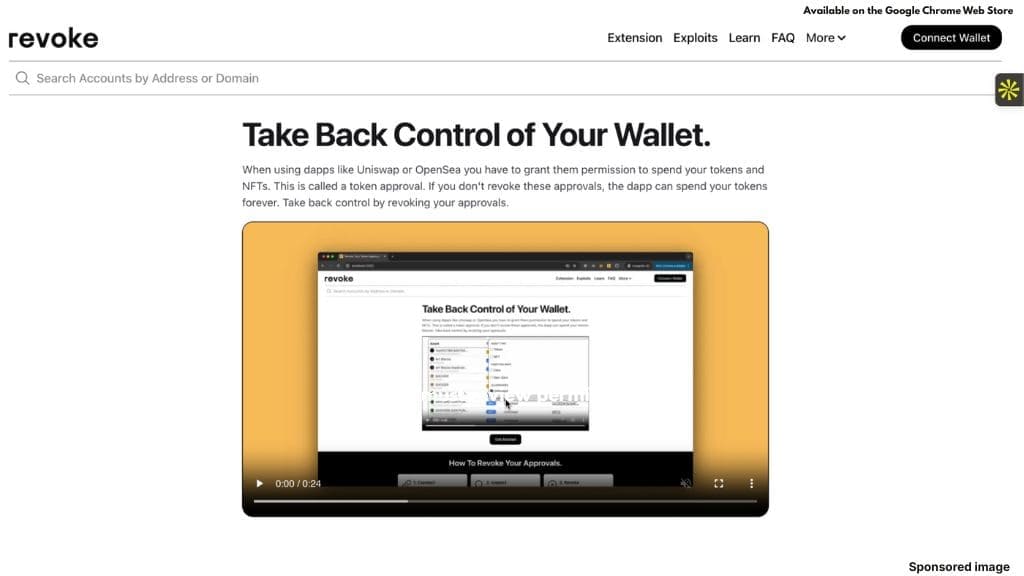
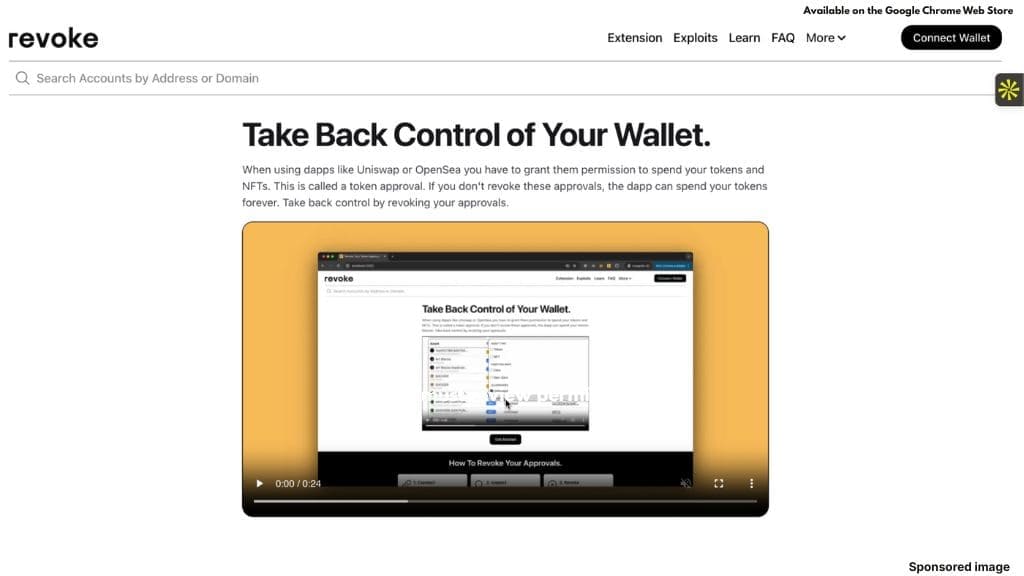
The platform shows all lively approvals related to a pockets, together with older permissions which will not be wanted. Customers can revoke or restrict these approvals to scale back publicity.
Revoke.money helps a variety of blockchains and Layer 2 networks. Its browser extension also can warn customers earlier than signing limitless approvals, encouraging extra managed permission settings.
4. Web3 Antivirus
Web3 Antivirus evaluates sensible contract code and assigns danger indicators primarily based on its construction and performance. It highlights options similar to upgradeable proxies, blacklist capabilities, or patterns related to identified exploits.


For NFT and token merchants, the device will help establish contracts with restrictive promoting situations or suspicious buying and selling conduct. Machine studying fashions evaluate new contracts in opposition to historic exploit information to flag similarities.
This sort of evaluation is especially helpful when interacting with newly launched tokens or lesser-known protocols.
5. Pockets Guard
Pockets Guard focuses on browser-level safety. It screens web sites and extensions for hidden scripts which will activate throughout pockets connections.
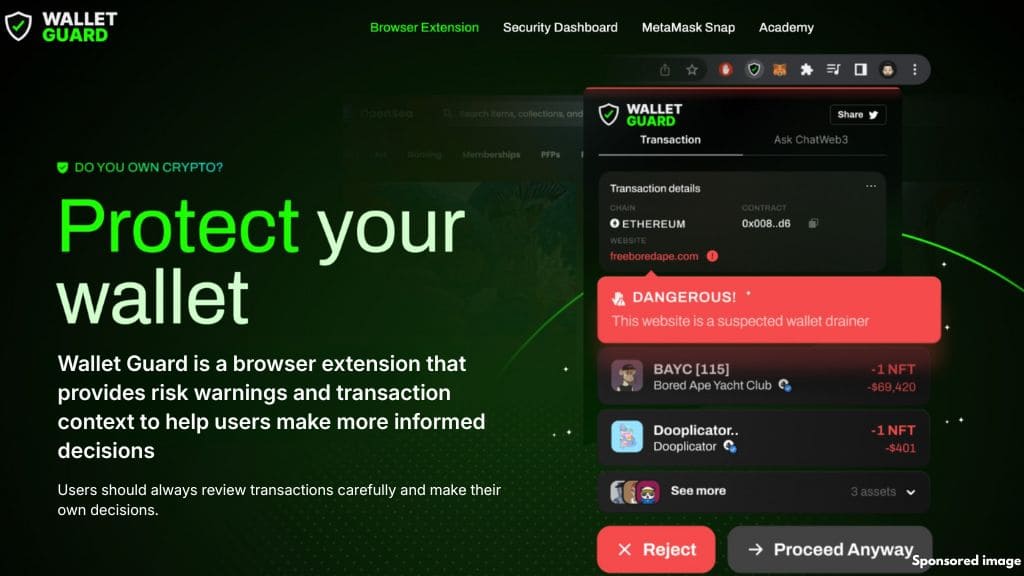
Its Storm Detection characteristic identifies malicious code embedded in in any other case legitimate-looking websites. The platform additionally gives a dashboard that summarizes pockets danger components, together with outdated approvals and previous high-risk interactions.
Pockets Guard maintains an actively up to date phishing database and integrates alerts immediately into the looking expertise, blocking entry earlier than interplay happens.
Conclusion
Web3 safety has developed past easy blocklists and handbook checks. Trendy threats require instruments that may analyze sensible contracts, permissions, and transactions in actual time.
Conventional safety software program doesn’t deal with the distinctive dangers of decentralized methods. Specialised Web3 instruments assist bridge this hole by offering transaction previews, approval administration, and contract evaluation earlier than irreversible actions happen.
A layered method stays the simplest technique. Combining real-time risk detection, transaction simulation, and common permission opinions can considerably scale back publicity to widespread Web3 dangers.
As blockchain ecosystems proceed to broaden, safety instruments should adapt alongside them. Understanding and making use of the proper protections is a necessary a part of collaborating safely in Web3 environments.
Press releases or visitor posts printed by Crypto Economic system have been submitted by firms or their representatives. Crypto Economic system just isn’t a part of any of those companies, tasks or platforms. At Crypto Economic system we don’t give funding recommendation, if you will spend money on any of the promoted tasks it’s best to do your individual analysis.







