On March 30, 2026, Google Quantum AI printed a new whitepaper revealing {that a} theoretical quantum pc may derive a personal key from a public key on the Bitcoin community in just some minutes. This timeframe intently aligns with Bitcoin’s 10-minute mining cycle, elevating the situation of an “On-Spend Assault” the place a transaction pending affirmation could possibly be intercepted and changed.
Moreover, Google consultants beneficial that blockchain initiatives full their migration to Put up-Quantum Cryptography (PQC) earlier than 2029 to safeguard digital signatures and transactions in opposition to sufficiently highly effective future quantum computer systems.
Understanding the Quantum Risk
The analysis illustrates a situation by which quantum computer systems may compromise the core safety mechanisms of Bitcoin and Ethereum. As a substitute of a direct assault on the pockets, this technique targets the general public key—which turns into seen on the blockchain throughout a transaction—to derive the non-public key, the last word issue controlling the belongings.
Present safety depends on cryptographic issues thought-about practically unattainable for classical computer systems to unravel, however which could possibly be considerably accelerated by quantum techniques. In line with Google’s estimates, a theoretical quantum system may carry out this calculation utilizing roughly 1,200–1,450 logical qubits and 70–90 million Toffoli gates, with a complete bodily qubit rely below 500,000 bodily—considerably decrease than earlier projections. These estimates have been validated utilizing the Zero-Information Proof (ZKP) technique.
In architectures using superconducting techniques, execution time could possibly be diminished to mere minutes. That is significantly vital as a result of public keys are sometimes uncovered solely through the transaction course of, making a slim window of vulnerability the place belongings could possibly be exploited if the non-public key’s derived quickly sufficient.
Nevertheless, the analysis emphasizes that quantum computer systems with adequate energy to execute this situation don’t but exist, and present estimates replicate capabilities below theoretical circumstances.
Inside Bitcoin’s 10-Minute Window
A main situation highlighted within the report is the “On-Spend Assault,” concentrating on transactions pending within the community’s mempool. As soon as a public key’s broadcast after a transaction is initiated, a theoretical quantum system may try and derive the non-public key earlier than the following block is confirmed.
With the Bitcoin community’s common affirmation time of 10 minutes, a “ready window” is created, permitting an attacker to compete instantly with the unique transaction. If the calculation is accomplished in time, they might broadcast a substitute transaction with the next price to make sure precedence inclusion within the block.
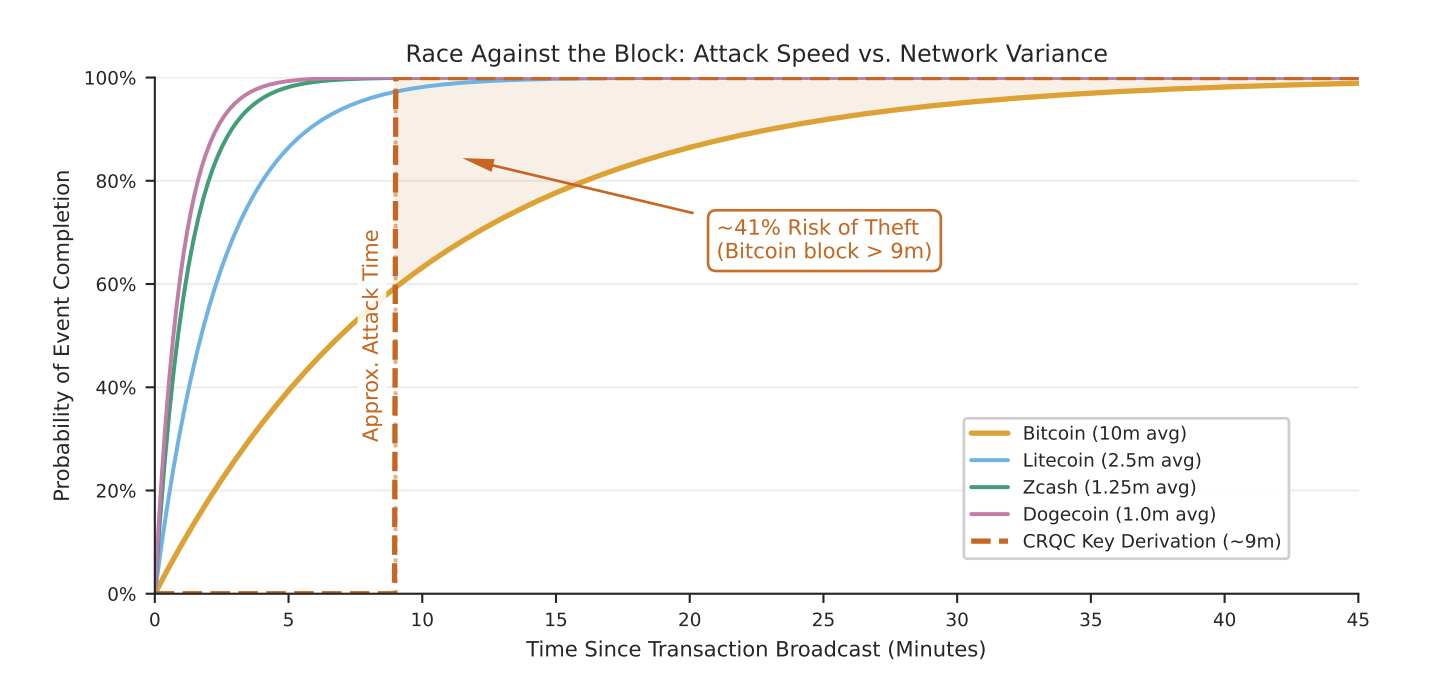
Race In opposition to the Block: Assault Pace vs. Community Variance. Supply: Google
Consequently, the success of such an intervention is strictly tied to the period of this window. Blockchains with shorter block instances, comparable to Litecoin (approx. 2.5 minutes), Zcash (75 seconds), or Dogecoin (1 minute), considerably slim the operational timeframe for an attacker.
Nevertheless, these estimates assume a non-congested community. In observe, an attacker may deliberately spike charges or flood the mempool to extend the likelihood of their fraudulent transaction being prioritized for affirmation.
The {Hardware} Hole — and the Race to PQC
Whereas estimates present a big discount in assault execution time, a cryptanalytically related quantum pc (CRQC) doesn’t but exist. Solely particular quantum architectures, comparable to superconducting techniques, can doubtlessly attain the speeds required for fast-attack eventualities, whereas different techniques stay restricted by processing constraints.
In a March 25, 2026 announcement, Heather Adkins, VP of Safety Engineering at Google, and Sophie Schmieg, Senior Workers Cryptography Engineer, said that the corporate goals to finish its transition to Put up-Quantum Cryptography (PQC) by 2029. This transfer is designed to guard encryption and digital signatures from future quantum-enabled adversaries.
This transition is significant for authentication techniques and digital signatures—the spine of blockchain transactions. Throughout this era, short-term mitigations embody limiting handle reuse and minimizing public key publicity.
Not All Dangers Are Equal
Pockets Publicity
The precise impression of the quantum risk varies throughout totally different pockets varieties, relying on whether or not the general public key has been beforehand uncovered on the blockchain.
- Weak Wallets: These embody legacy P2PK (Pay-to-Public-Key) addresses or wallets training handle reuse, the place the general public key’s already publicly out there.
- Decrease-Threat Wallets: Trendy codecs comparable to P2PKH (Pay-to-Public-Key-Hash) or Taproot supply higher safety, as the general public key’s hashed and solely revealed in the intervening time of spending.
System-Stage Dangers
For Bitcoin, the chance is concentrated in “dormant” addresses with uncovered public keys which can be not energetic. An estimated 1.7–2.3 million BTC fall into this class. If exploited, this huge quantity of belongings may re-enter the market, creating vital strain on the circulating provide.
On Ethereum, the impression is broader because of the ecosystem’s reliance on good contracts and administrative keys. Roughly 20.5 million ETH in giant wallets have uncovered public keys, whereas admin keys for stablecoins, bridges, and oracles may signify vital factors of failure if compromised.
Below Ethereum’s Proof-of-Stake (PoS) mechanism, controlling greater than one-third of the staked ETH may disrupt finalization, whereas a two-thirds threshold permits for management of the consensus mechanism. If validator non-public keys are compromised, these thresholds turn into targets, elevating the chance from particular person wallets to the whole community infrastructure.
Conclusion
The Bitcoin community is just not presently below direct assault, as sufficiently highly effective quantum {hardware} stays a future improvement. Nevertheless, new estimates present that the hole between assault functionality and transaction processing time is closing, regularly eroding the system’s security margins.
Comparable dangers prolong to Ethereum and different blockchain platforms, the place the assault floor is bigger as a consequence of advanced good contract infrastructures. On this panorama, transitioning to Put up-Quantum Cryptography (PQC) has turn into a necessary step in securing digital signatures and blockchain integrity for the long run.







