TL;DR
- North Korea’s regime has stolen greater than $2 billion in cryptocurrencies in 2025—virtually triple final 12 months’s whole, in response to Elliptic.
- The $1.46 billion Bybit hack represents the 12 months’s largest single loss.
- Hackers are actually focusing on people and company funds via social engineering and complicated money-laundering schemes.
North Korea has stolen over $2 billion in cryptocurrencies to date in 2025, in response to a report from Elliptic, which attributes the assaults to teams linked to the regime, together with Lazarus.
This new determine is almost triple that of 2024 and units a brand new annual document, with three months left within the 12 months. Because the regime started its cyber-crime operations within the crypto business in 2017, the cumulative whole has surpassed $6 billion.

The Bybit hack, which came about in February and is estimated at $1.46 billion, accounts for many of this 12 months’s losses and ranks among the many largest incidents within the sector’s historical past. Elliptic additionally attributes to North Korea the assaults on LND.fi, WOO X, and Seedify, together with greater than thirty smaller breaches affecting exchanges and DeFi platforms. The agency’s report aligns with analyses from the United Nations and intelligence businesses, which state that the stolen funds finance Pyongyang’s nuclear and missile packages.
The examine reveals a transparent shift within the regime’s techniques. Whereas centralized platforms stay a main goal, hackers are more and more specializing in rich people and company funds.
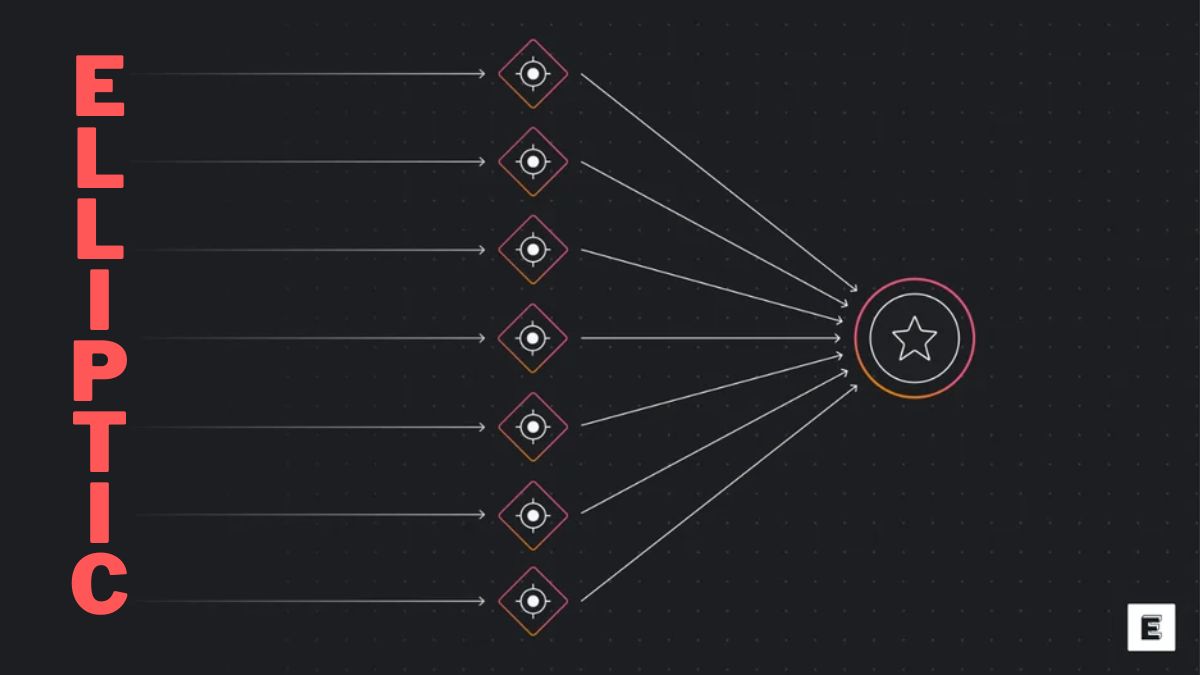
Elliptic: The Weak Level in Safety Is Human
This 12 months’s market rebound has made these targets extra enticing, as they typically lack the institutional safety infrastructure that protects main platforms. The assaults now rely totally on social-engineering strategies—deception, faux job presents, and impersonation on social networks—to acquire keys and pockets entry. Elliptic maintains that the weak level in crypto safety is now not technological however human.
As fund-tracking capabilities enhance, North Korea’s laundering networks have gotten more and more refined. Following the Bybit assault, the stolen funds went via a number of rounds of swaps between Bitcoin, Ethereum, BTTC, and Tron, utilizing obscure protocols and tokens issued by the hackers themselves.


New laundering strategies now embody successive mixing rounds, cross-chain transactions, and the creation of tokens designed to hide the origin of stolen property